Contents
Physical layer security techniques promise information-theoretic security for wireless communication, i.e., these techniques are designed to be provably secure against eavesdroppers.
This course discusses the theory and practice of physical layer security. The underlying theory is introduced and the application of these fundamentals towards practical solutions is discussed. Attacks against (practical) physical layer security techniques are presented. Theoretical and practical exercises, as well as the presentation of selected recent research results by seminar talks of students, further deepen the understanding of the subject matter. Contents:
- Properties of the physical layer
- Fundamentals of information-theoretic security and delineation from cryptography
- Physical layer security techniques (such as cooperative jamming, orthogonal blinding, zero-forcing, interference alignment, key extraction)
- Practical aspects of physical layer security techniques
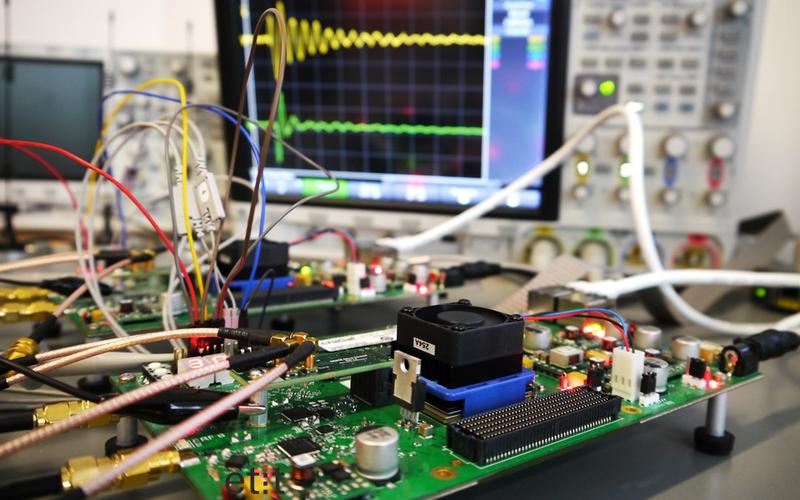
- Practical implementations of physical layer security techniques using software-defined radios
- Selected current approaches to physical layer security
Objectives
Students attending this course familiarize themselves with theoretical and practical knowledge in the area of physical layer security. They are able to describe the most important information-theoretic basics as well as the theory and practice of physical layer security techniques. They are able to analyze practical physical layer security techniques and describe their weaknesses. Students gain competencies in the practical realization of physical layer security techniques. They acquire the current state of research on physical layer security and can present it in a comprehensible fashion by means of technical seminar presentations.
Prerequisites
This is a challenging and advanced course. We recommend that all students attending PhySec have attended CriCom before. (It is also fine to take CriCom in parallel to this course.) In particular, we strongly recommend the following background knowledge:
- Signal Processing (e.g., signal analysis, Fourier transform, modulation schemes, I/Q components)
- How to program using MATLAB
- Basic knowledge of IT-Security (e.g., security goals)
If you do not have this background knowledge, this course might be too hard for you, as you will have to learn a lot of topics that PhySec depends on. It might be better to first learn the above skills and then take PhySec.